A Guide To Data-Mining Scraping With Proxies
With an ocean of information on the internet, it gets challenging to find the right kind of data needed. Numerous techniques are being used around the world to collect relevant data from millions of pieces of information available. Data mining is one of the most useful methods for collecting data. It is helping us make better analysis by having related data without much tedious work.
What is Data Mining?
Data mining refers to the collection of data and the extraction of particular patterns from that set of data. It lets you identify the data of your requirement so that you can work on that specific part only, instead of going through all the sources. Data mining helps find potentially useful patterns.
Data mining has shifted the burden from entirely manual work to statistics, Artificial Intelligence, database technology, and machine learning. The combination of all these tools enables us to discover unknown relationships among the data. The obtained knowledge through data mining will help to decrease cost, increase revenue, reduce risks, database marketing, fraud detection, etc.
Process of Data Mining
The method of data mining consists of six necessary steps:
The business understanding the initial step for data mining involves business understanding. Business understanding means to understand the needs of the client and define your goals accordingly.
- Data Understanding
The next step is to understand the data through the collection of data through several sources.
Along with searching for the data, it is also essential to ensure the properties of the data that they match our requirements.
2. Data Preparation
Data preparation means to prepare the data for usage. Data is processed by adding in any missing pieces of information or values, or by canceling out the noisy data. The process takes around 90% of the total time of the project.
3. Data Modeling
In this process, we use statistical and mathematical models to evaluate the data patterns collected. Several kinds of techniques and models can be made into use to determine validity.
4. Evaluation
The findings from the data models prove helpful against the pre-determined goals. The evaluation carried out in this phase lays the basis of the decision for the implementation of the plan.
5. Deployment
In the last stage of the process, a detailed plan for monitoring, shipping, and maintenance is developed and shared with business operations and organizations.
The process usually ends with the generation of a report that shows the findings and experiences of the project. Such a statement can help the organization to enhance the strategies and business policies.
Data mining Techniques
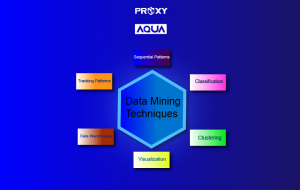
Data mining is an excellent tool for finding and evaluating the right data for your business requirements. There are many techniques used for this purpose, owing to the feasibility of the organization or the team. These techniques make use of AI, machine learning, and database management to provide the best results.
- Classification
The classification data mining technique involves the categorization of the data according to different features and attributes. By the identification of various characteristics of the data and understanding the ones needed for the purpose, organizations can evaluate the data based on these attributes.
- Clustering
Unlike classifications, clustering makes use of graphics to understand the attributes of the collected data relating to the metrics. These graphical representations comprise of colors and color schemes to highlight the distribution and relation. The colors and graphics make it quite helpful for the identification of data and relevant trends.
- Visualization
Visualization is another technique used in data mining that makes use of colors for data representation. The visualization tools used nowadays are also useful for streaming data. Dashboards used in visualization are a frequently used tool to get insights into the data. It can be an excellent alternative to the use of mathematical or statistical methods.
- Data Warehousing
The orthodox use of data warehousing involved the storage of data for dash-boarding abilities and reporting. But now, they are an essential part of the data mining process as developments have occurred that have made it possible to use the method for data mining. Some semi-structured and cloud data warehouses provide an in-depth analysis of the data.
- Tracking patterns
The tracking of patterns is a vital part of the process and widely used technique as well. The identification and monitoring of trends play an essential role in an organization for business outcomes and goals. The tracking tools can help to create products similar to an ongoing trend or stock the original patterns for the demographic.
- Sequential patterns
Sequential patterns help to uncover the events in a sequence. These patterns can help you determine the data regarding the customer’s need for products in order of occurrences. It can aid the company in launching more goods in its product line and expand its business.
Use of Proxy for Data Mining
Data mining is assisted by proxy servers nowadays to ensure the smooth running of the process. Commonly Residential IPs and a pool of IPs proves remarkable for the purpose.
Benefits of using a proxy for data mining
The benefits of using a proxy for data mining include:
- Hiding your IP address
One of the most excellent benefits proxy servers provide, include hiding your IP address. While carrying out any such process on the internet, there are chances of getting banned for repeating the operation several times. To save yourself from any such problem, you can use a proxy that hides your IP address. Without the visibility of your IP address, it would not be possible for anyone to track or ban you. However, while using a residential proxy, make sure that you select the correct region.
- Protection
As the proxy helps to hide your original identity, it saves you from online frauds and hackers. The number of online scams is increasing tremendously, and one should take significant measures to ensure the safety of the device and system. A firewall can assist additionally to filter any such attempt of hacking.
- Stable connection
If you don’t know this one, you would be pleased to know this fantastic benefit of using a proxy for data mining. Data mining is a lengthy process, and it can take notable time for it to finish. But, what if your connection goes off or fluctuates? It can be tiresome and troubling. As the proxy does not use your link, preferably some anonymous one, it can help you have a stable connection without any issues.